Hi, I’m wondering how best to set up my Freedombox on my home network to maintain maximum security for the other machines on the local network?
Possible Solution?
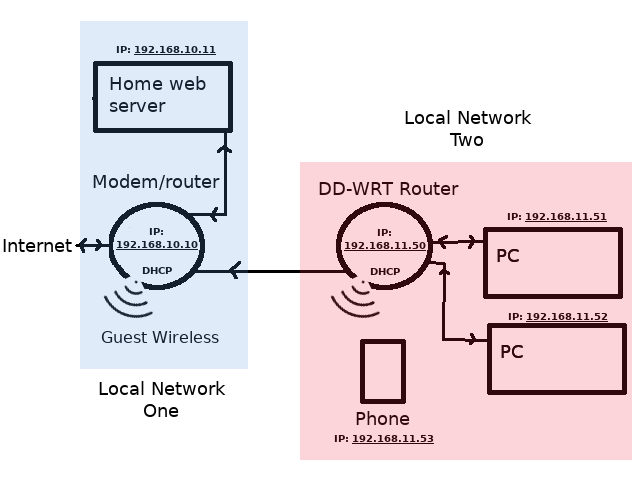
I found the following previous part answer to a different issue, which makes me think I should have my Freedombox setup as a DMZ device?: “This is typically done by logging into the router, and configuring DMZ ip address as FreedomBox IP address (after making a reservation for that IP address).” [Solved] Problems configuring DMS
Background
I’m looking at this because I had my Freedombox connected to my local network as a standard device, with ports forwarded to it by my home router. But I noticed yesterday that the web root index.html page had been changed (cracked!): /var/www/html/index.html The index.html had been clanged to point to an external website. Because I was obviously going to notice this change I assume it was a white-hat cracker warning me that my system was vulnerable!
I’m not too surprised because I have been doing a lot of messing about with the Freedombox machine: opening ports, not being careful enough about what info I provided on support posts on StackOverFlow etc. And I had also installed Wordpress and NextCloud in the web root and hadn’t looked at hardening either install. So there was probably too much information out on the web about how to find my machine and its configuration. And it was probably unnecessarily vulnerable. However, finding evidence that the machine has been cracked has made me consider my network security far more seriously!
Thanks for any advice with this